
Private investigators’ help may be necessary for individuals, small businesses, couples, organizations, or police departments due to a variety of reasons. Although their services may differ, you can often find them to have skill sets that will analyze information and uncover evidence that verifies facts. Find out more about fact-checking on this site here.
Regardless of their niche, most of them are experts in research, interviews, documentation, surveillance, and undercover investigation. They can work in polygraph departments, computer forensics, criminal investigation, retail loss and prevention, pre-employment screenings, missing person services, and more.
Sometimes, these experts generally work alongside the police and other law enforcement to track the movements of a suspect, or they can uncover missing children, insurance fraud, etc.
About an Employee Background Check
Before employing someone, companies may sometimes conduct a thorough background check on their chosen candidates. They will want to verify someone through their social security numbers, as well as check for information like their criminal records, vehicle registration, medical history, drug test results, sex offender cases, military duties, driver’s license, and work history. The extensiveness or coverage of the check will depend on the job that is involved and the corporation.
New hires may need their information to be gathered, whether it is through publicly available sources or covert means. However, these situations can be very complex, and they require extensive inquiries that may be carried out by PIs from sites like https://deltafirminvestigations.com/ and get the services that you need. Collection and analysis of data to vet potential candidates, study what your competitors are doing, and maintain brand image is possible with them.
Infidelity and Adultery Investigation
Marital problems are common, but if you suspect that your significant other is having an affair, you might want to confirm the facts. In cases like these, know that confusion, betrayal, and a mix of other emotions can cloud your judgment. Certainty is priceless if you are on the way to confronting the other person. Consultations are provided, and you need to choose a firm that has agents all over the country, so you will not have any problems in a specific jurisdiction.
During times of excessive use of the computer, unconfirmed overtime hours, hiding of their smartphones, defensive behaviors, lack of sexual interest, going out with friends like they are single, and removal of your picture on their Facebook accounts, this might be the best time for you to check what they are really up to.
Messenger activities, emails, and other communication mediums are going to be part of the investigation, and the team that will handle the case is going to use complete discretion with their work. Of course, complete confidentiality is part of the package, and photos may be included.
If you are married, and there is even a small suspicion of infidelity, you will need photographs, thorough documentation, or video clips if the situation leads to divorce. All of the pieces of evidence that will be collected will be factual, and there is no interference involved. Know that the investigators’ aims are to help, and they know that their clients deserve to know the truth, so they act accordingly.
What are the Processes Involved?
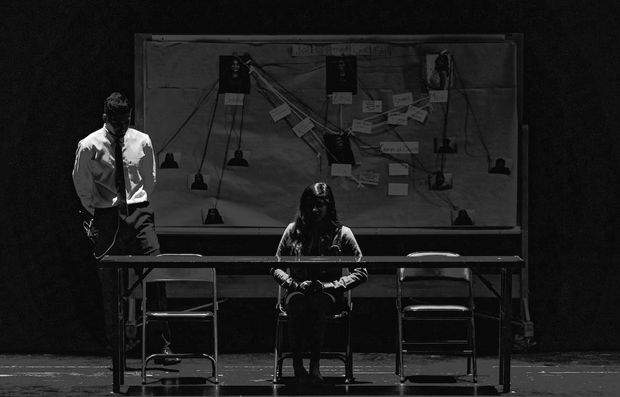
In movies, books, and pop culture, people think that PIs are those who are hiding in the shadows with long mustaches, pipes, and glasses to hide their identities. However, you might now get their services through the internet, and they look like your regular guy in a sea of people going about their businesses.
Generally, their primary goal is to provide proof of wrongdoing, and they get more information from bystanders who might have witnessed the incident. Sherlock Holmes, in books, may assume a fake identification, tails his man for days, and looks for clues in the neighborhood. However, how much of his work is really true?
One of the first steps that will help a client become successful is to separate the facts from fiction. Most experts are often retired law enforcement officers who know the boundaries of their state laws. They know they cannot prosecute or arrest any criminals and they are essential in providing information to solve crimes.
Self-employment is common with them, and they work for various credit collections and financial institutions. Corporate investigators specialize in trademarks, patents, and intellectual property theft, while CPAs can see if there’s fraud in a company’s transactions. Get more info about credit and PIs at this link here: https://www.private-investigator-info.org/credit-report.html.
In reality, many of them are busy finding missing relatives or friends or doing skip tracing. Skippers may gather civil records, court hearings, address history, credit reports, employment, deep web data, tax records, property documents, and phone numbers to locate someone. They will also get in touch with relatives if someone fails to show up in court, find journalists or lawyers for a legal case, or track down debtors who have damaged property.
Recruiters may also hire them to conduct an identity check for a specific individual at a surface level or navigate social media for info or check genealogy websites. Know that the investigator’s jobs are perfectly legal, as long as they do not break the laws when gathering information. Using violence to obtain what they need or making a white lie to read a financial report is not considered valid in court. The best professionals already know what is allowed and not allowed, so you do not risk committing a crime as a client. The average time for gathering data can be 48 hours, but tracking an individual can sometimes take a few weeks. Most of them have databases that can help them start the process but check their reviews beforehand.